| Disclaimer: Microsoft Azure AD is a product offered by Microsoft Corporation. This document shows how to configure applications in Azure AD using Microsoft Azure Portal. What is shown here is valid at the time of writing and can be referred to as a guide line to understand how applications should be setup in Azure AD. This can change over time. Please refer to the latest Azure AD documentation for more up to date information. |
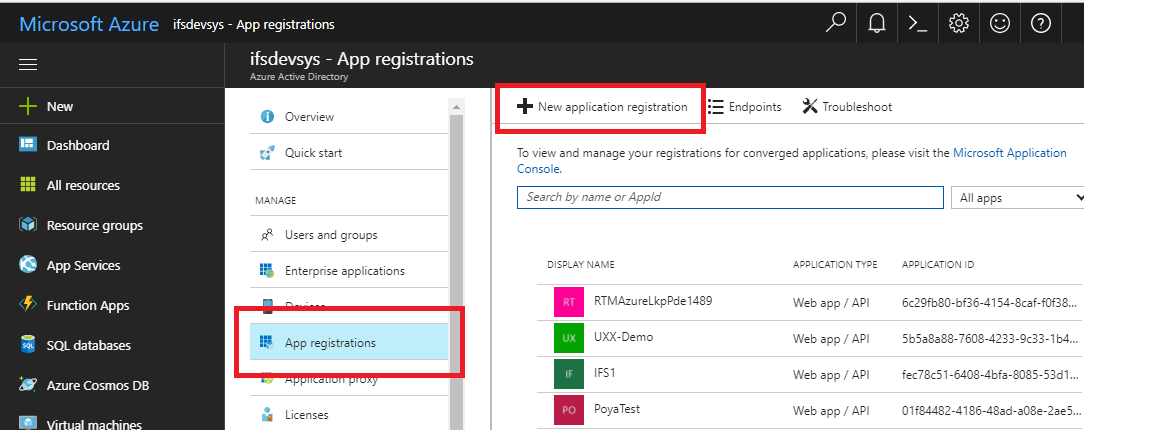
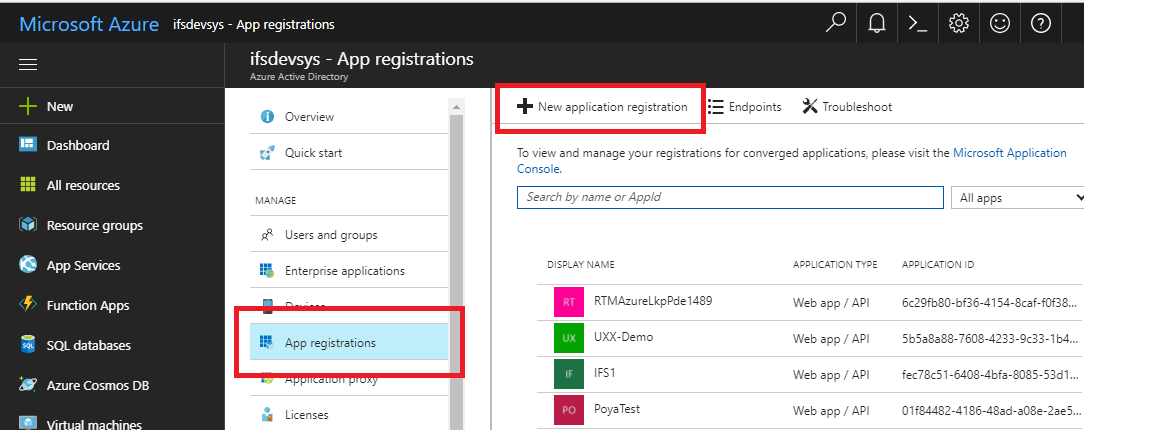
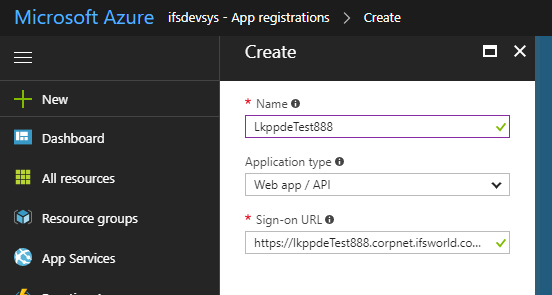
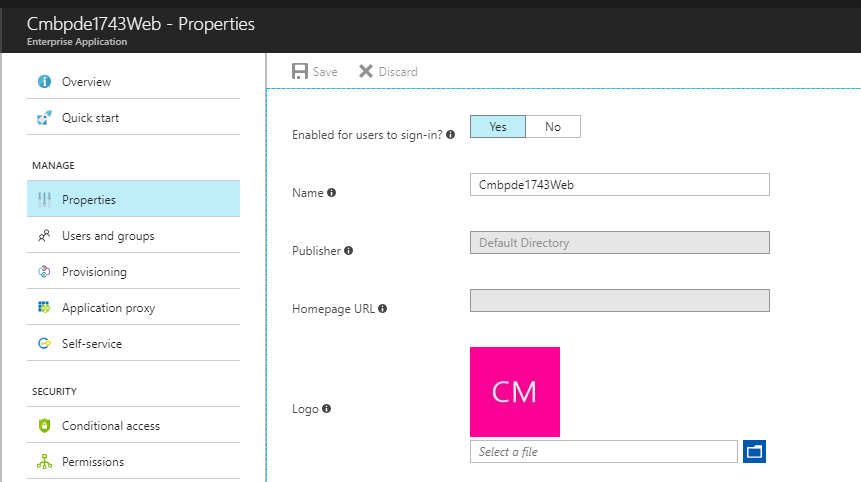
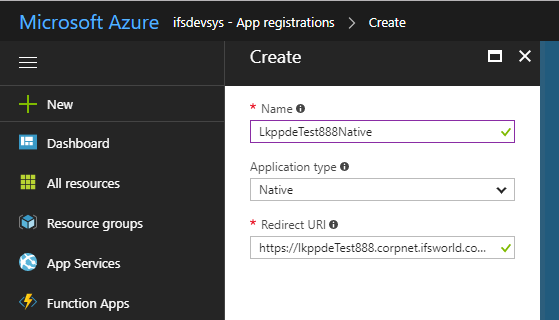
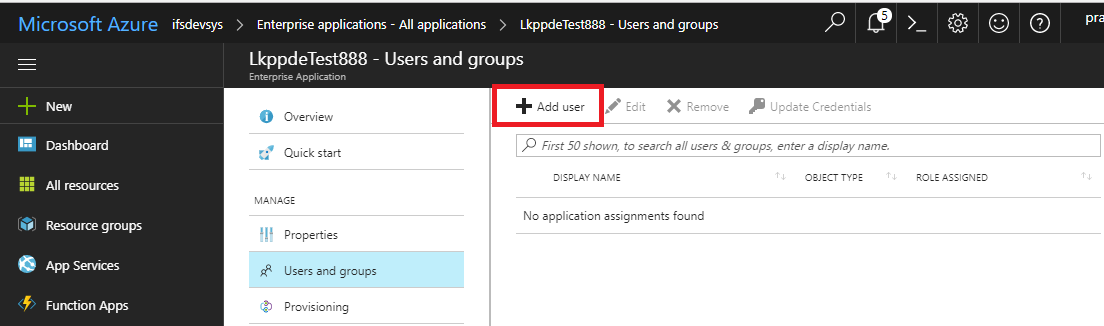
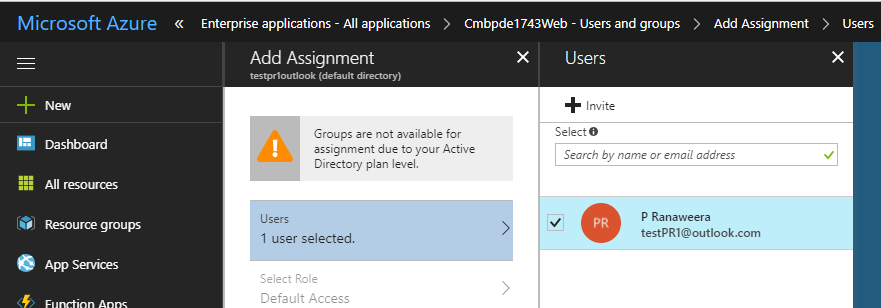
To authenticate user logins for Aurena client a new Web application / API needs to be added in Azure App registrations.
https://<fully_qualified_domain_name_of_the_app_server:port>main/ifsapplications/projection/oauth2/callback/
https://<fully_qualified_domain_name_of_the_app_server:port>/main/ifsapplications/web/oauth2/callback/
e:g:
https://lkppdeTest888.corpnet.ifsworld.com:58080/main/ifsapplications/projection/oauth2/callback/
https://lkppdeTest888.corpnet.ifsworld.com:58080/main/ifsapplications/web/oauth2/callback/
https://<fully_qualified_domain_name_of_the_app_server:port>/b2b/ifsapplications/projection/oauth2/callback/
https://<fully_qualified_domain_name_of_the_app_server:port>/b2b/ifsapplications/web/oauth2/callback/
e.g.: https://lkppdeTest888.corpnet.ifsworld.com:58080/b2b/ifsapplications/projection/oauth2/callback
https://lkppdeTest888.corpnet.ifsworld.com:58080/b2b/ifsapplications/web/oauth2/callback
https://fully_qualified_domain_name_of_the_app_server:port>/int/default/plsqlgateway/oauth2/callback
https://fully_qualified_domain_name_of_the_app_server:port>/int/default/clientgateway/oauth2/callback
https://fully_qualified_domain_name_of_the_app_server:port>/main/default/plsqlgateway/oauth2/callback
https://fully_qualified_domain_name_of_the_app_server:port>/main/default/clientgateway/oauth2/callback
e:g:
https://lkppdeTest888.corpnet.ifsworld.com:58080/int/default/plsqlgateway/oauth2/callback
https://lkppdeTest888.corpnet.ifsworld.com::58080/int/default/clientgateway/oauth2/callback
https://lkppdeTest888.corpnet.ifsworld.com::58080/main/default/plsqlgateway/oauth2/callback
https://lkppdeTest888.corpnet.ifsworld.com:58080/main/default/clientgateway/oauth2/callback
NOTE: Re-authenitcation behavior: When the user logs in and work in IFS Enterprise Explorer client the client session is refreshed based on the session timeout (Default 10 minutes). When the current session times out the Access Token given by the ADFS server is used to refresh the client session. The Access Token is has a lifetime of about 1 hour by default. Once the Access Token is expired the Refresh token given by the ADFS server is used to obtain a new Access Token. The Azure AD Refresh token has a very long lifetime of about 90 days according to Azure AD documentation. Once the Refresh token is expired it will not be possible to get any new Access Tokens. So re-authentcation will fail and the user will be prompted for credentials.
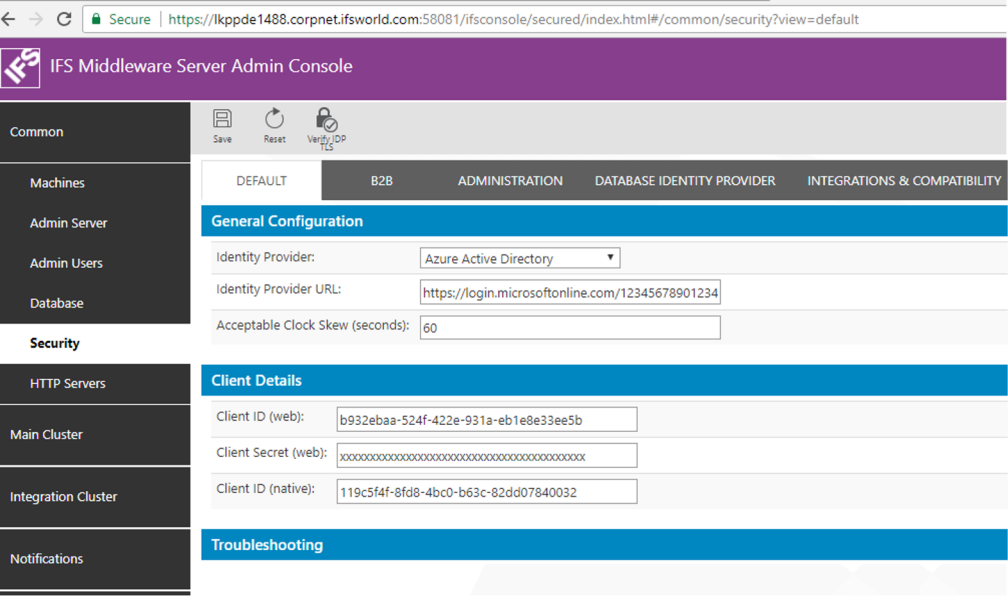
After the applications have been added to Azure AD as explained in the above section, some configurations are needed in IFS Middleware Server Admin Console to finish setting up IFS Applications to use Microsoft Azure AD as the Open ID Connect Identity Provider.
Login to IFS Admin Console. Go to "Common > Security".
The DEFAULT tab holds the Open ID provider configuration details for Aurena client and the native applications. Select "Azure Active Directory" as the Identity Provider. Fill in the details as show below.
Parameter Value Identity Provider Azure Active Directory Identity Provider URL https://login.microsoftonline.com/<tenant_id>*
Note: tenant_id here is the Azure tenant id of your organization.
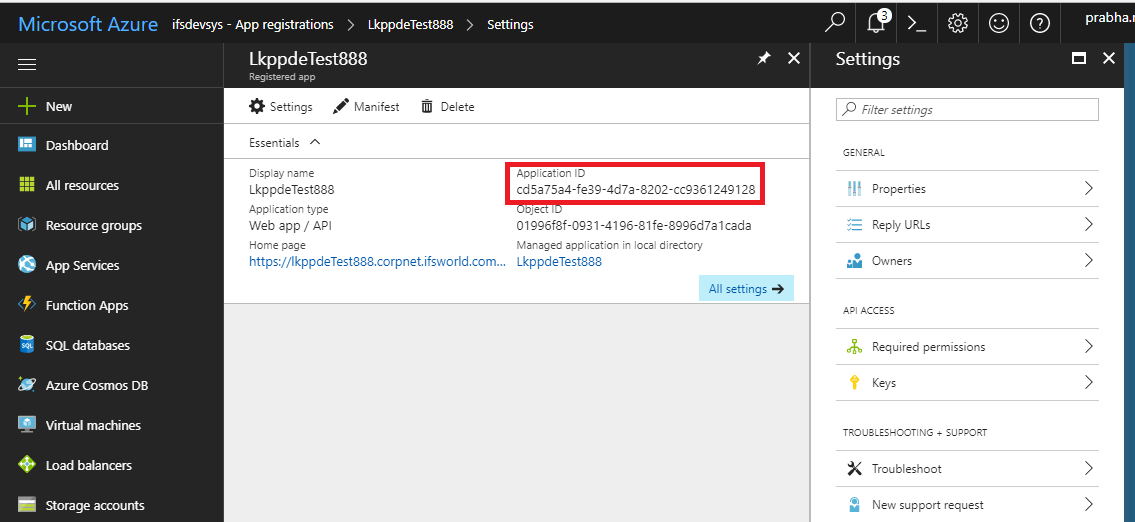
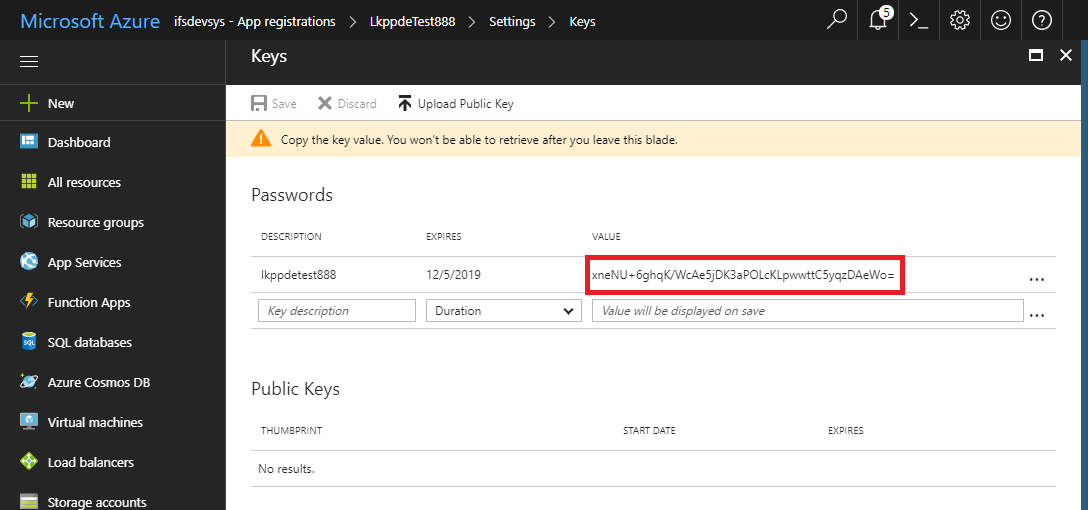
Alternative to the tenant_id you can use the name of the Azure Active Directory with the domaiin (e.g: https://login.microsoftonline.com/ifsdevsys.onmicrosoft.com)Acceptable Clock Skew (seconds) This will be the tolerated amount of clock skew when the validity of the token is calculated. E.g.: 60s Client ID (web) Application ID taken from Azure AD app registration when Aurena Web application was registered. Client Secret (web): Security Key generated when Aurena Web application was registered in Azure AD Client ID (native): Application ID taken from Azure AD app registration when IFS Enterprise Explorer and Toch apps were registered as a Native application.
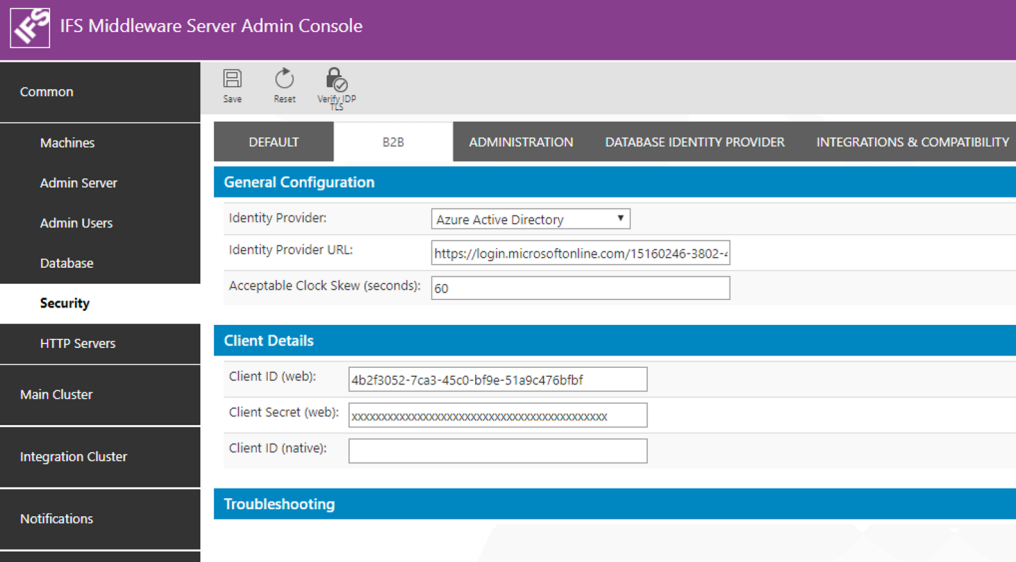
The B2B tab holds the Open ID provider configuration details for B2B client. Select "Azure Active Directory" as the Identity Provider. Fill in the details as show below.
Parameter Value Identity Provider Azure Active Directory Identity Provider URL https://login.microsoftonline.com/<tenant_id>*
Note: tenant_id here is the Azure tenant id of your organization.
Alternative to the tenant_id you can use the name of the Azure Active Directory with the domaiin (e.g: https://login.microsoftonline.com/ifsdevsys.onmicrosoft.com)Acceptable Clock Skew (seconds) This will be the tolerated amount of clock skew when the validity of the token is calculated. E.g.: 60s Client ID (web) Application ID taken from Azure AD app registration when B2B Web application was registered. Client Secret (web): Security Key generated when B2B Web application was registered in Azure AD Client ID (native): Leave this blank as there is no native application for B2B.
* How to find the <tenant_id> :
In Azure Portal click on the Azure Active
Directory. From the middle blade select "Properties". The properties of the
Azure Active Directory will open up in the right most blade. The field "Directory
ID" gives the Tenant Id of the the Azure Active Directory.
IFS Applications have a user registry of its own in the Oracle Database. These users are know as Foundatoin1 Users. A user authenticated from an External Identity Provider such as Azure AD needs to be mapped to a Foundation1 user for him to get access (authorization) to the application. The Foundation1 users are listed in the table FND_USER_TAB. The DIRECTORY_ID field of this table is used for the mapping between the external user identity and the Foundation1 user identity.
When Azure Active Directory is used as the user repository the email address of the user in the Azure AD (the login id used by the user to login to the Azure AD) must be the value that should be entered as the value for DIRECTORY_ID field.
If Azure Active Directory is enabled with Domain Services so that the AD is accessible using LDAPS protocol, the Active Directory Synchronization process can be used to synchronize users registered in the Azure AD to Foundation1 users.
To get functions such as Security Check Points to work in an environment where Azure AD is used as the Open Identity Provider it is required to enable Secure LDAP (LDAPS) in the Azure AD. In order to configure LDAPS the Azure AD has to be configured as a Azure AD Domain Service. You need a valid Azure Subscription to be able to do so. Following documentation provided by Microsoft Azure gives step by step instructions on how to do this: https://docs.microsoft.com/en-us/azure/active-directory-domain-services/active-directory-ds-admin-guide-configure-secure-ldap
Once you have successfully enabled Domain Services in Azure AD you will get a Secure LDAP External IP Address. You can communicate with the Azure Active Directory using the LDAPS protocol and perform functions such as user authentication using LDAPS. Now it is possible to configure the Compatibility AD authenticator to be the Azure AD.
In IFS Admin Console go to Common > Security and select the tab "Integrations and Compatibility". Fill in the details as given below for Active Directory Authenticator:
| Parameter | Value |
|---|---|
| Enabled | Tick to enable |
| Hostname | Input the Secure LDAP External IP Address obtained after enabling Domain Services in Azure AD. If domain name resolution is in place you should be able to use the Azure AD domain name here as well. |
| Use SSL | Tick to enable. |
| Port | 636 (Since LDAPs) |
| Username | When configuring the Domain Service an Admin user is added to the Admin Group AAD DC Administrator in Azure AD. Put that user name here. Use the format user@azureADdomain (e.g. adminuser@testdomain.onmicrosoft.com). |
| New Password | The user's password |
| User Base DN | This can remain blank |
| Group Base DN | This can remain blank |
More information on Compatibility Active Directory Authenticator can be found here >>.